
Hello, reader! It’s week 8 of what I calculate to be a 34 week journey to the PWK class and OSCP exam. This time around we’ll talk about chapter 8 in Georgia Weidman’s: Penetration Testing. I won’t be showing many of the exploits from this chapter because it can get repetitive after a short while.
Exploitation
In short, this section compliments chapters 5 (Information Gathering) and 6 (Finding Vulnerabilities) well as the “next step” in the kill chain. In chapters 5 and 6 we proceed with enumerating the target. We look for potential vulnerabilities, interesting ports, indicators of weakness, and mixed with a little Google-fu, we find exploits for old versions of software. The amount of enumerating one might do would depend on the scope and time allotted for the penetration test. In chapter 8 we take the next step and execute exploits on our vulnerable machines and software.
WebDAV
The first exploit I’ll talk about from this chapter is a WebDAV vulnerability present in XAMPP instances from 1.7.3 and earlier. WebDAV (Web Distribution Authoring and Versioning) is an extension of HTTP that allows remote administration of a web server. It works by defining a set of new HTTP methods that define actions that a WebDAV responsive module should respond too on a server. The vulnerability that we’re exploiting here isn’t anything particularly technical. On versions 1.7.3 of XAMPP and earlier, WebDAV was turned on by default and had some default credentials (wampp/xampp). Now-a-days, WebDAV is disabled and has a random password instead. We can use metasploit to perform this exploit or just do it manually with cadaver. cadaver is a unix WebDAV command line interface client.
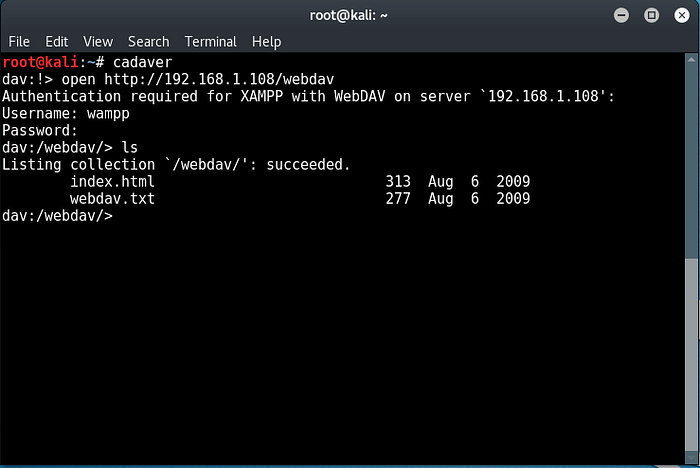
We would sign in with the default credentials and upload a web shell. A web shell is a “backdoor” of sorts that executes commands passed to it. This would allow us to do some post exploitation such as setting up user accounts to remotely sign into the machine, staging a meterpreter shell, etc.
Zervit
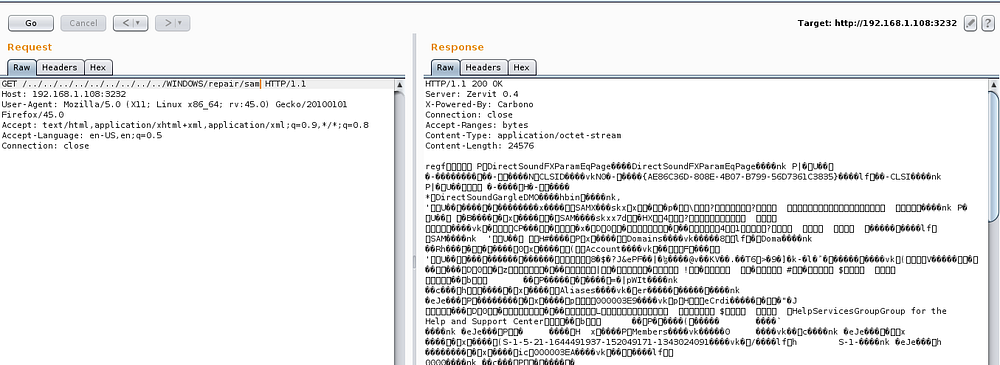
The next exploit I’ll show is, again, an issue of unpatched or old software. Zervit is a simple-to-setup web server. All the configuration occurs when you start it up; it’s limited to two configuration choices: port number and whether or not to list directories. While this particular vulnerability is not hard to find, a simple Google search on the version of Zervit in the lab reveals a Directory Traversal vulnerability (not even a clever one like the ones in IIS 4, 5, and 6!). In this instance, I’ll use the directory traversal vulnerability to pull out the SAM (Security Account Manager) file.
Open NFS Shares
In chapter 6, the reader will discover an open NFS mount using an NMap script on the Ubuntu target machine. In chapter 8, we actually “exploit” this operation security vulnerability by mounting the system to our machine. To mount this system, execute mount -t nfs -o nolock <ip>:/export/georgia /tmp/mnt. This might work for you, but I found trouble with it initially. If you’re having problems with mounting an NFS system, try executing apt-get install nfs-common and then mounting. This worked for me.

SLMail
While there are a couple of vulnerabilities that exist in this particular installation of SLMail (such as user enumeration), we’re more interested in a buffer overflow exploit that was can easily be found on exploit-db. We can also find an entry on Rapid7 which indicates that there’s a metasploit module available exploit/windows/pop3/seattlelab_pass. I haven’t had time to investigate the action mechanism of this vulnerability much at the moment so I’m limited to using metasploit for it.
Closing Remarks
I’ve not been feeling super well for the past week so this week’s content is a little lacking. For instance, I wanted to add a section with an example of why you shouldn’t roll your own crypto where I show off Wiener’s Attack or another weakness in certain values of p in Diffie-Hellman key exchanges. We’ll see what next week holds. I’ll try to get two chapters minimum.
See ya next week!
